Resources

Blog & News

How to Be Successful with Desktop-as-a-Service, Part 2 - Security, Endpoints, Management, and Culture
How to Be Successful with Desktop-as-a-Service, Part 2 - Security, Endpoints, Management, and Culture

WRITTEN BY
TABLE OF CONTENT
- Identity management and security
- Endpoint devices
- Workspace and application management
- Company culture
Identity Management and Security
DaaS platform providers should be able to deliver secure and easy access to applications and desktops using modern identity systems such as Microsoft Azure AD, Okta, and Google, and Single Sign-On (SSO) using multi-factor authentication. Security processes—from user authentication to malware protection to software updates—should be as transparent as possible to users. Onerous or invasive security procedures can have a negative impact on users. It also needs to be crystal clear who is responsible for what to avoid any possible gaps in security.
Look for a provider that integrates with your existing identity authentication provider (IDP) and SSO to streamline user access and minimize user disruption as you transition.
If you’re in a regulated industry such as healthcare, financial services, or government, look for a provider that is not only certified to meet the relevant regulations for your industry but that has direct experience serving it.
Endpoint Devices
Endpoint devices enable end-users to see and interact with the virtual application or desktop. When it comes to endpoint devices, there is no one-size-fits-all strategy. For some of us, the browser is the new OS, while for others the endpoint device and its operating system remain important.
DaaS solutions such as Xi Frame allow you to run almost any application in an HTML5-compatible browser. This approach supports a broad range of endpoint devices, unlocking use cases that were impossible with previous approaches. When implemented correctly the user experience is great and functionality is high.
With many DaaS solutions, apps and desktops are delivered via a provided client, receiver, or agent. In this case, you have to be sure that the necessary software is available for all endpoints you need to support and that the software can be easily accessed, installed, and managed.
Key endpoint-related questions for DaaS success:
- What is your endpoint device strategy?
- Are endpoint devices managed, and, if so, how?
- Can you leverage a browser to access virtual apps and desktops or do you need to install a specific client which embeds itself into the device?
- Do you have special external devices attached that are needed by virtual apps and desktops?
- What devices does the DaaS platform support?
Workspace and Application Management
I touched on this topic in a previous blog, but I’m coming back to it because it’s so important to DaaS success—and so easy to overlook during the DaaS decision-making process. Unless your chosen DaaS provider offers a completely managed service, there are some tasks that your team will remain directly responsible for.
This likely includes everything to do with the guest OS, applications, and user workspace:
- Windows OS patches
- Application deployment, configuration, licensing, updates, and integration with back-end services
- User performance monitoring
- Anti-virus and other security-related solutions within the guest OS
- Windows user profile management
The beautiful thing about many DaaS solutions is that you can leverage the knowledge, technology, and processes you already have, while taking advantage of the various solutions the DaaS provider offers, such as centralized image management, Windows user enterprise profile containers, and user experience monitoring.
When you choose a DaaS provider, you’ll want to find out what options they offer, and how easy (or hard) the available tools will be for you to utilize. This includes:
- Does the DaaS provider support public cloud and on premises infrastructure? Which providers and platforms?
- Which identity management solutions are supported out of the box?
- Is the DaaS service multi-tenant with RBAC by design?
- What’s the process for managing and updating applications?
- Can your existing workspace and application management solutions be reused? Do you want to reuse them, or is it better to re-evaluate?
- Does the provider support virtualized desktops and/or virtualized applications?
- Does the provider support persistent or non-persistent desktops?
- Does the DaaS solution include easy-to-use capacity management, image management, and scaling?
- Does the provider have public, documented APIs to automate workflows and integrate applications into a workspace?
Company Structure and Culture
I’ve left potentially the thorniest issues for last. Your decision-making process should factor in both your company’s structure and culture.
If your company’s culture is risk- or change-averse—or if you’ve had VDI projects that have failed in the past—DaaS can help overcome these obstacles, allowing you to start small and scale as quickly or slowly as necessary. Choose a compelling use case, set up the environment, onboard applications, and invite end-users for that use case to try it out. Evaluate the user and administrator experience and complete a business case and TCO/ROI calculation for a larger rollout or the next use case. I have seen great success across enterprises of all sizes who started small and adapted quickly using DaaS.
Learning More
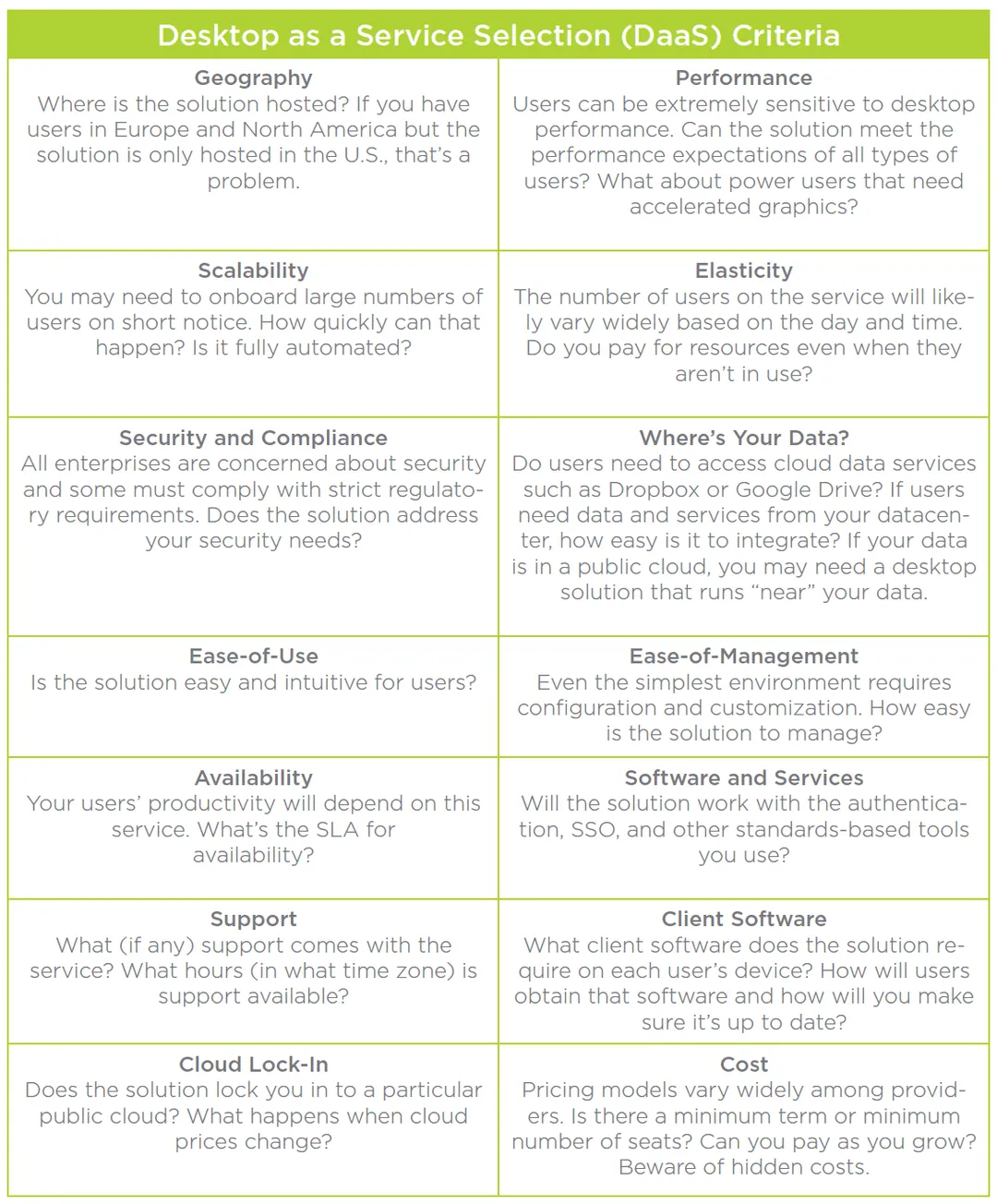
In this two-part blog I’ve tried to outline some of the factors that will help you choose the best DaaS solution for your organization and plan your deployment. However, this is a big topic, and there is a lot to think about. The table above includes a number of additional factors that may be important in your decision.
This table is drawn from a recent eBook: The Definitive Guide to Desktop-as-a-Service. If you want to learn more, the introductory chapters of this book discuss the benefits of DaaS and have additional information on picking a service.
The book goes on to discuss the capabilities of Nutanix Xi Frame, a unique DaaS solution from Nutanix. In the next blog, I’ll explore Xi Frame use cases and capabilities.
